Managed IT Solutions

At Gateway TelNet, we believe that a first-rate IT environment should be a business enabler — not a business challenge.
Our experienced virtual Chief Information Officers (vCIOs) deliver and manage a secure, scalable and dependable IT environment based on your unique business needs. We monitor and update your IT environment 24x7x365 — from firewall to smartphone — with over 600 certified Network Operations Center (NOC) technicians to proactively identify and address potential issues.
We manage all aspects of IT for our clients by proactively monitoring, managing and supporting your IT infrastructure so you don't have to.
Our dedicated vCIOs are knowledgeable and experienced advisors with the ability to meet ongoing IT needs, respond quickly to incidents and plan strategically. They help leverage new IT technologies for growth, efficiency and customer satisfaction.
We have certified and sought out the best in the industry and have built a support model with complete transparency, giving clients an intuitive view into their IT infrastructure performance through regular reporting.
LAN Optimization
LAN Optimization is paramount to delivering an enterprise quality voice and cloud experience. Our highly skilled vCIOs leverage state-of-the-art tools to proactively monitor and analyze network components over a work-cycle test period. We then leverage critical data, including MOS scores, to identify and remediate any issues related to voice quality, latency, packet loss and other critical variables that will affect voice or data quality for any supported applications.
Pro-Active 24x7 Help Desk
We have over 600 certified and highly-trained technicians supporting your own assigned virtual Chief Information Officer (vCIO), your trusted advisor who reviews and addresses your specific needs. Our technical support team will quickly and efficiently resolve even your most complex technical problems over phone, email, web-based chat or onsite. Whether you're dealing with hardware, software or network issues, our team will work with you until the problem is solved.
Enterprise File Sync & Share
Secure your corporate data anytime, anywhere. Our file sync allows you to sync sensitive corporate files between servers, laptops, desktops, smartphones, tablets and the cloud so you have fluid collaboration and mobile productivity securely under control.
Office 365 Options
From home to business, desktop to web and all the devices in between, you can access your files, create and collaborate on documents in real-time and utilize the tools you need to keep your business moving.
Managed WiFi
Wireless accessibility and security is no longer a no-win, either/or choice. We leverage best-of-breed technology to implement and secure enterprise grade WiFi capabilities for our customers. We recognize the need for employees to move between locations and be able to cut the string.
Our cutting edge technology allows us to provide wireless security for accessing corporate data as easy as it is to provide complimentary wireless access for clients in a mall, while ensuring that security is maintained at all levels. Our enterprise grade WiFi management technology also allows us to integrate with existing active directory infrastructure, while providing an easily configurable and usable interface for administrators to see who is connected and what physical areas they are connected to. We take the guess work out of wireless security and package it to suit your needs.
Security as a Service & Managed Firewall
Security as a Service has become a huge concern for businesses and we have invested heavily in our capabilities. We offer 24x7x365 firewall administration and monitoring for all security events. Using our cutting edge Unified Threat Management (UTM) capability, we are able to provide a security overlay which provides whitelisted updates to firewall rules in a non-invasive manner. The advantage of this security overlay is that our customers are protected at the firewall and user levels from hacking, phishing, adware, malware and Trojans.
In addition to perimeter security, we deploy a dual layer of AV and Malware protection on every device we manage. Our strategic deployment methodology is recognized as the hallmark against ransomware and all the crypto strains. We pride ourselves in delivering a comprehensive security as a service offering that is second to none in the industry.
Mobile Device Management
We provide powerful and secure monitoring and management of mobile devices that enable iPhones, iPads, Notebooks and Androids to securely access your corporate network. Our MDM platform is fully-managed to provide flexible approaches for enrollment, asset management, policy enforcement and the distribution of profiles, apps and docs based on device ownership. We work to help manage and secure these devices, with centralized policy and compliance control from a web-based console.
Business Continuity & Disaster Recovery
Our comprehensive backup and disaster recovery solutions provide robust data protection, secure and reliable cloud storage, automatic anti-virus and patch management, and a range of local and hybrid solutions. Our solutions are about more than just backup — they're designed to quickly revive your network following any unplanned downtime.
Cloud Services
We use leading technology and security standards to safely provision servers, networks and storage resources. Our secure, web-based clouds can handle the most rigorous production workload while providing the autonomy, control, security and visibility that your business requires. We offer public, private and hybrid cloud options.
Cloud Workspace as a Service
Our cloud workspace as a service solution acts identically to the desktop you use today, except it now stays in the cloud. Whether you're at the office, traveling for business or working from home, simply access it from any connected device to work with your files and applications.
Is Your Business HIPAA Compliant?
This year over 2 million healthcare facilities, law firms, accountants and other businesses that perform services for health care related companies are being targeted for HIPAA/HITECH Act Phase 2 compliance audits by the U.S. Department of Health & Human Service. Not performing annual HIPAA compliance assessment is a HIPAA violation and subjects you to finds of $50,000 per record.
Gateway TelNet's HITECH Compliance Assessments and Compliance-as-a-Service offerings help get and keep you HIPAA complaint. Our HIPAA Compliance-as-a-Service offering builds on our baseline HIPAA and PCI Risk Assessment to support ongoing compliance for your environment.
PCI compliance failure can result in losing your right to accept credit cards. Our PCI Compliance Assessments and Compliance-as-a-Service offerings produce initial and ongoing support to comply with Payment Card Industry Data Security Standards (PCI DSS).
Contact us today to schedule your FREE HIPAA and/or PCI risk assessment and consultation.
CyberSecurity
With the Gateway Telnet Cybersecurity Bundle we are able to offer;
- Managed Firewall Protection: Intrusion Prevention-URL Filtering-Gateway Antivirus-Spam Prevention-and Application Control.
- Dark Web software: Dark Web Threat Alerts-Compromised Data Tracking and Reporting
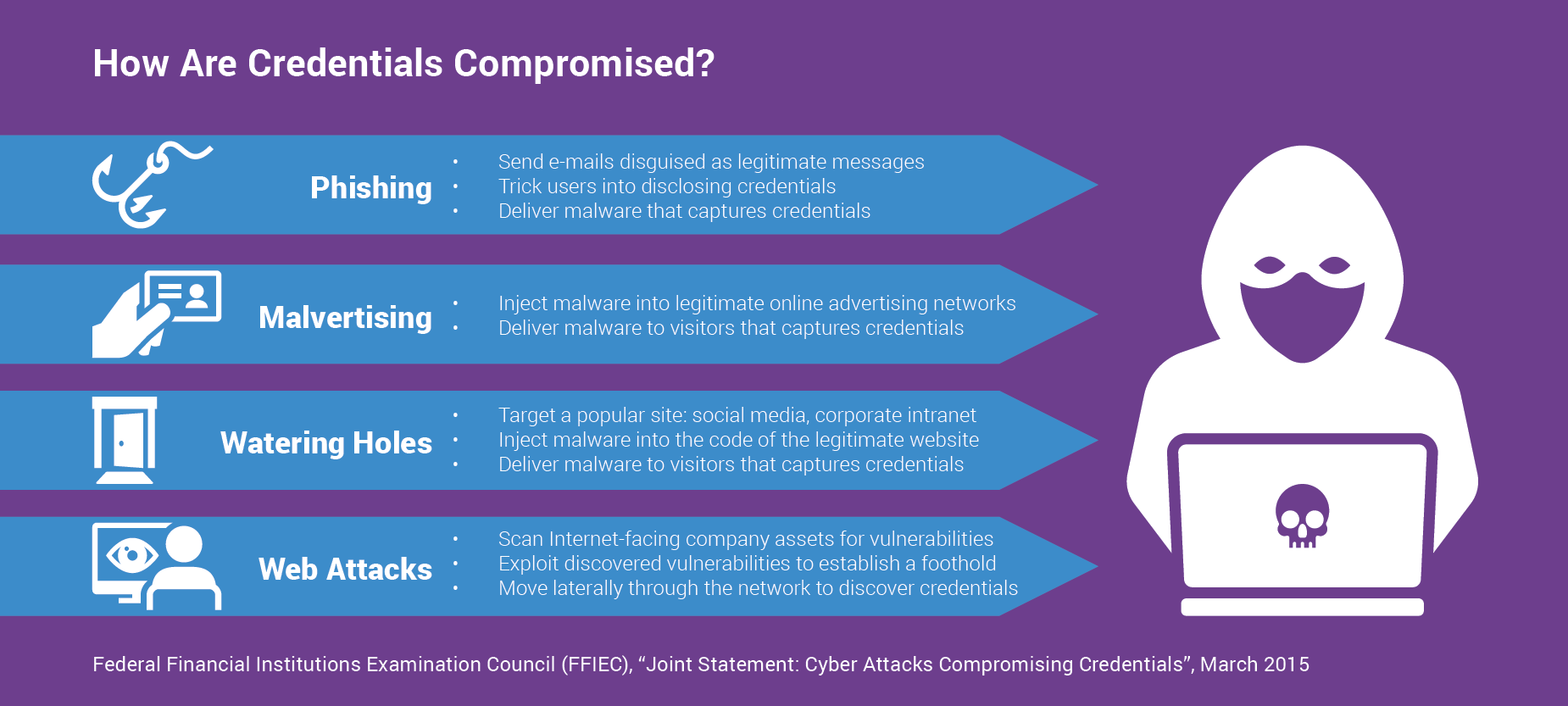
- Security Software: Endpoint protection-DNS Protection-Training Awareness Program-Fake Phishing campaign
- Endpoint Protection: Advance virus and spam protection-Skeptic scanning for spam, malware, phishing and targeted attacks.
